Case In-depth Analysis
Conduct a multidimensional analysis of significant or complex scam cases, including the operational process, technical methods, psychological manipulation strategies, and more.
JPEX Fraud Case
Introduction
In September 2023, Hong Kong uncovered a large-scale fraud case involving the virtual asset trading platform JPEX. This company, which claimed to be legitimate and regulated, lured over 1,600 investors into devastating losses through false promises of high returns and a complex financial pyramid scheme. The total amount involved in the case exceeded HKD 1.2 billion. This incident not only revealed the high risks associated with virtual currency investments but also sparked widespread discussions on financial regulation.
Case Background
JPEX was established in 2020, positioning itself as a global digital asset crypto trading platform. The fraud was orchestrated by the company’s founder, Mr. Li, Chief Financial Officer, Mr. Zhang, and Technology Head, Mr. Wang. Through extensive advertising and promotions by well-known key opinion leaders (KOLs) such as Lam Chak and Chen Yi, the platform successfully attracted a large number of investors. JPEX claimed its platform token, JPC, could offer high returns and encouraged investors to purchase and stake JPC in large amounts.
Fraud Process
- Initial Promotion
- Advertisements and Promotions: Advertisements and Promotions: JPEX placed extensive advertisements across various media channels, claiming that its platform token JPC offered lucrative investment opportunities with high returns. The highly enticing advertisements garnered significant attention.
- KOL Endorsements: Prominent KOLs like Lam Chak and Chen Yi leveraged their public influence by frequently sharing success stories of high investment returns on social media. These endorsements attracted a large number of fans and investors.
- Attracting Investments
- False Promises: JPEX claimed that its platform token JPC could generate high returns in a short period of time, enticing investors to purchase and stake JPC in large amounts. Investors, drawn by the promise of high returns, poured significant funds into the platform.
- Unlicensed Operations: Despite not having a license from the Securities and Futures Commission (SFC), JPEX falsely presented itself as a legitimate platform, misleading investors. The SFC had been monitoring the virtual asset sector since 2017 and listed JPEX as an unlicensed company and suspicious website in July 2022, yet JPEX continued its illegal operations.
- Operational Tactics
- High Returns: In the early stages, some investors did receive high returns, which further attracted more people to invest. However, these initial returns were actually paid using funds from later investors.
- Raising Transaction Fees: After the SFC issued warnings, JPEX increased its withdrawal fees to USD 999, while the withdrawal cap was set at only USD 1,000. This effectively restricted investors from withdrawing their funds. Many investors discovered they could not successfully withdraw their money, leading to growing suspicions about the platform.
- Halting Transactions: During the police investigation, JPEX abruptly shut down its financial management pages and ceased all transactions, leaving investors unable to operate or retrieve their funds.
- Case Exposure
- SFC Warning: On September 13, 2023, the Hong Kong Securities and Futures Commission (SFC) issued a warning statement, pointing out that JPEX was unlicensed and operated in a suspicious manner. The SFC expressed particular concern about JPEX’s aggressive promotional tactics and identified serious issues with its operational model.
- Police Action: On September 18, 2023, Hong Kong police launched a large-scale enforcement operation codenamed "Iron Gate," raiding multiple JPEX offices and arresting eight individuals, including Lam Zuo and Chen Yi. During the operation, police searched several offices, uncovering large amounts of cash, luxury jewelry, and documents related to JPEX.
Investigation and Arrests
The police and SFC jointly held a press conference to disclose detailed information about the case. As of that time, the police had received 1,641 reports, with the total amount involved reaching HKD 1.187 billion. The police noted that JPEX used advertisements, media, over-the-counter (OTC) exchange shops, and key opinion leaders (KOLs) to promote the platform, enticing investors to register and trade cryptocurrencies. By controlling users’ cryptocurrency private keys, JPEX effectively gained full control over their assets.
Detailed Relationships of Key Figures
- Li (Unnamed): Founder and CEO of JPEX, the mastermind behind the entire scam, responsible for overall strategy and direction.
- Zhang (Unnamed): Financial director of JPEX, in charge of managing the company’s cash flow, ensuring the scam proceeds were smoothly transferred and concealed.
- Wang (Unnamed): Technical director of JPEX, responsible for platform maintenance and user data management, ensuring smooth operation and handling technical issues.
- Lam Zuo: A well-known KOL who promoted JPEX through his significant influence, attracting a large number of investors. He frequently posted success stories of high-return investments on social media to bolster the platform’s credibility.
- Chen Yi: Another prominent KOL tasked with promoting JPEX via social media platforms, increasing its exposure and perceived trustworthiness to lure unsuspecting investors.
Dialogue Scenarios
Scenario 1: Investor Inquiry
Investor A: "Lam Zuo, I saw you recommending the JPEX platform. Does JPC really offer such high returns?"
Lam Zuo: "Of course! I’ve invested a lot myself, and the returns are fantastic right now. Hurry up and join—you don’t want to miss this opportunity!"
Scenario 2: Withdrawal Issues
Investor B: "Why is there a $999 withdrawal fee? And I can only withdraw $1,000—this is totally unreasonable!"
Customer Service: "This is our new policy to ensure the platform’s security and liquidity. Please understand."
Victim Demographics Analysis
The victims included 1,129 males and 512 females, aged between 18 and 49. Most were inexperienced investors drawn in by promises of high returns, having invested significant sums. Key characteristics of the victim group include:
- Lack of Investment Experience: Most victims had little understanding of virtual asset investments and were easily swayed by promises of high returns.
- Middle-Aged and Young Adults: Victims were primarily aged 18–49, indicating this age group is more receptive to emerging investment channels but lacks strong risk assessment skills.
- Blind Trust: Many victims learned about JPEX through social media and KOL endorsements, blindly trusting so-called “investment experts” without conducting proper background checks or risk evaluations.
- Eagerness for Quick Wealth: Victims generally exhibited a desire to get rich quickly, making them vulnerable to scams promising “high returns, low risk” while ignoring potential dangers.
Case Issue Analysis
1. How did the scammers use new communication technologies to achieve their goals?
The scammers leveraged new communication technologies in the following ways:
- Social Media: They used platforms like Facebook, Instagram, and Twitter to create appealing profiles, share success stories, and connect directly with potential victims. In the JPEX case, KOLs like Lam Zuo and Chen Yi used their influence to legitimize the platform.
- Online Advertising: Targeted ads were placed on Google, YouTube, and social media, using algorithms to reach individuals interested in investments and high returns.
- Instant Messaging Apps: Apps like WhatsApp, Telegram, and WeChat facilitated direct communication with potential victims, allowing scammers to build trust through personalized messages and real-time interaction.
- Fake Websites and Emails: Professionally designed websites and phishing emails deceived individuals into believing they were dealing with a legitimate entity. JPEX’s polished website enhanced its credibility, making it easier to mislead investors.
2. What were the common attraction tactics in this case?
The scammers employed the following common tactics:
- High Returns: Promises of guaranteed, high investment returns with minimal risk. For example, JPEX offered exceptionally high JPC returns, luring inexperienced investors.
- Authority and Trust: Leveraging endorsements from influential figures and presenting the scam as a credible, established business. Endorsements from Lam Zuo and Chen Yi boosted JPEX’s trustworthiness.
- Scarcity and Urgency: Creating a sense of urgency with limited-time offers or claims that the investment opportunity was about to close, prompting victims to act quickly without due diligence.
- Exclusivity: Suggesting the investment was exclusive and not open to the public, making targets feel privileged and more inclined to participate.
- Complexity: Using convoluted terminology and investment strategies to confuse and impress targets, making the scam appear more legitimate.
3. What are the linguistic characteristics of this scam?
The linguistic features of this scam include:
- Persuasive and Convincing Tone: The content was carefully crafted to be highly persuasive, presented in a confident tone, and bolstered by authority and data to enhance credibility.
- Emotional Manipulation: Exploiting victims’ emotions—fear, greed, and the desire for quick wealth—to drive irrational investment decisions.
- Technical Jargon: Employing complex financial and technical terms to obscure actual risks and increase trust among victims unfamiliar with the domain.
4. How can similar scams be prevented?
Methods to prevent such scams include:
- Education and Awareness: Raising public awareness about common scam tactics and prevention techniques to improve risk recognition.
- Background Checks: Conducting thorough due diligence before investing, including verifying a platform’s legitimacy and reviewing SFC warnings.
- Skepticism of High Returns: Staying rational and cautious of promises of high returns with low risk—every investment carries risks, and high rewards typically mean high risks.
- Professional Consultation: Seeking advice from qualified financial advisors or lawyers before making significant investments.
- Vigilance: Remaining alert and skeptical of unfamiliar investment opportunities, avoiding impulsive decisions driven by temptation.
Conclusion
The JPEX scam highlights the high risks and complexities of virtual asset investments. Through meticulously designed tactics, JPEX successfully lured numerous investors, resulting in massive financial losses. This case underscores the importance of strengthening financial regulation and public education to prevent similar incidents. Investors must remain vigilant and exercise caution to avoid becoming the next victims.
Mainland Students Coming to Hong Kong Fraud Case
This case study is summarized from fraud cases found on the Xiaohongshu (Little Red Book) app.
Related Links:
Case Link 1 Case Link 2 Case Link 3 Case Link 4 Case Link 5
Story Background
Many victims are young people who have recently arrived in Hong Kong. They receive a call from an unknown number. Through a series of carefully designed steps, scammers gradually lure these victims into a trap, ultimately attempting to defraud them of their money.
Detailed Description of the Scam Process
Initial Contact and Fear Creation
- Sudden Call from a Stranger
- Victims receive a call from an unknown number, starting with Cantonese before switching to a Mandarin recording. The caller claims to be from the Hong Kong Immigration Department or the Hong Kong Communications Authority, informing the victim that their mainland ID has been misused and is linked to a criminal case or financial crime. The victim immediately feels the situation is serious and becomes nervous.
- Intimidation and Building a Tense Atmosphere
- The scammer uses a stern tone and detailed case descriptions to heighten the tension. For example, the scammer might say: “Your mainland ID has been misused and is involved in a serious criminal case. To avoid affecting your normal life in Hong Kong, you must cooperate with the investigation immediately.” Such statements make the victim feel the situation is urgent and in need of immediate resolution.
Phone Transfer and Professional Terminology
- Transfer to a Fake Police Station
- The call is then transferred to someone claiming to be from a mainland police station. In this stage, Scammer B uses professional terminology and a serious tone to apply further pressure. For instance, the fake officer might say: “Hello, this is the Shanghai Public Security Bureau. We’ve discovered that your ID was used for illegal activities in Shanghai. To verify your identity, please provide detailed personal information.”
- Detailed Inquiries and Identity Verification
- Scammer B asks for detailed personal information such as ID numbers and home addresses, informing the victim of specific illegal activities tied to their ID. For example, Scammer B might say: “Your ID was used to open bank accounts involved in money laundering. We need to further verify your identity, so please answer truthfully.”
Forged Official Documents and "Education"
- Providing Fake Official Documents and Education
- After gaining the victim’s initial trust, the scammer provides forged official documents and images, even conducting so-called “education.” These documents appear official and professional, such as fake police badges or case records. The scammer may also provide videos or articles on “protecting personal information” to further lower the victim’s guard.
- Increasing Psychological Pressure
- The scammer continues contacting the victim via phone, claiming the case is extremely serious and must be resolved quickly. For example, a fake supervisor might say: “Your case involves a wide scope and is highly complex. We recommend you take immediate action, or the consequences will be unimaginable.”
Persistent Intimidation and Pressure
- Ongoing Calls and Communication
- The scammer maintains psychological pressure through constant calls and messages. Victims are asked to download specific software like Zoom or WhatsApp and participate in so-called “online statements” via video or text. Scammer D might say: “For your safety, we need you to report your location and activities every three hours and send selfies or photos of your surroundings.”
- Describing the Severity of the Case
- The scammer elaborates on the case, emphasizing its severity and urgency. For example, a fake police captain might say: “Your ID has been used in multiple criminal activities involving huge sums of money. To prove your innocence, you must fully cooperate with our investigation.”
Demanding Money
- Gradual Introduction of Financial Demands
- After earning the victim’s trust, the scammer starts making financial demands, claiming a deposit or transfer to a “safe account” is needed to prove the victim’s innocence. A fake financial officer might say: “To protect your rights, we need you to transfer a sum of money to our secure account. This is only temporary custody and will be fully refunded after the case is closed.”
- Applying Further Pressure
- Using forged official documents and a stern tone, the scammer pressures the victim to quickly gather funds. For example, a fake prosecutor might say: “If you can’t provide the deposit in time, we’ll have no choice but to take legal action against you.”
Intervention by Friends/Family and Truth Revealed
- Intervention and Warnings from Friends/Family
- At a critical moment, the victim’s friends or family may step in, warning them of a possible scam. For instance, a friend might say: “Are you sure this is a real police officer? There are tons of similar scams online—be careful!”
- Reflection and Recognizing the Scam
- After hearing advice from friends and reflecting, the victim begins to realize the scam’s existence and decides to report it to the police while taking steps to protect their personal information and assets. For example, the victim might say: “Something feels off about this—I’m going to the police.”
- Reporting and Preventive Measures
- Once aware of the scam, the victim promptly reports it to the police and takes steps to safeguard their personal information and assets, such as changing bank card passwords or freezing accounts. They may also share their experience to warn others. For example, the victim might say: “I almost got scammed—everyone, be careful and don’t trust unknown calls!”
Character Relationships and Role Analysis
- Initial Contact (Scammer A)
- Role: Claims to be from the Hong Kong Immigration Department or Communications Authority.
- Responsibility: Initiates contact and instills fear to create tension.
- Fake Police Officer (Scammer B)
- Role: Poses as a mainland police officer after the call transfer.
- Responsibility: Builds credibility by detailing the case and requesting identity verification.
- Fake Supervisor (Scammer C)
- Role: Pretends to be a higher-ranking official.
- Responsibility: Provides fake education and assistance to lower the victim’s guard.
- Fake Police Captain (Scammer D)
- Role: Claims to be an experienced police captain.
- Responsibility: Uses professional terms and emotional tactics to maintain psychological pressure.
- Fake Prosecutor (Scammer E)
- Role: Poses as a prosecutor.
- Responsibility: Reinforces the scam’s severity with an authoritative tone and complex dialogue.
- Fake Financial Officer (Scammer F)
- Role: Pretends to be a financial officer.
- Responsibility: Guides the victim on transferring money and provides fake official documents.
Dialogue Scenario Analysis
- Intimidation and Establishing Authority
- Scammers use official language and detailed case descriptions to make victims feel the situation is serious and urgent.
- Example Dialogue:
- Scammer A: “Hello, this is the Hong Kong Immigration Department. We’ve found that your mainland ID was misused in a criminal case. You need to report this immediately.”
- Victim: “What? What’s going on? What should I do?”
- Scammer A: “Don’t worry, we’ll transfer you to the police. Just follow their instructions.”
- Psychological Manipulation and Emotional Tactics
- Scammers use professional jargon and emotional appeals to gradually erode the victim’s caution, drawing them into a psychological trap.
- Example Dialogue:
- Scammer D: “Hello, I’m a police captain. We’ve caught the main suspect, but we need more information from you. Please download Zoom and add me for a statement.”
- Victim: “Okay, I’ve downloaded it.”
- Scammer D: “For your safety, please report your location and activities every three hours and send selfies or photos of your surroundings.”
- Persistent Intimidation and Fake Documents
- Through forged documents and constant contact, scammers make the case feel real and urgent.
- Example Dialogue:
- Scammer E: “Hello, I’m the prosecutor. Your case has been escalated to us. We need a deposit to ensure your cooperation and safety.”
- Victim: “I can’t get that much money right away—I need time.”
- Scammer E: “The situation is urgent. Please gather the funds quickly, or we’ll have to take legal action.”
- Intervention by Friends/Family and Self-Reflection
- Prompted by friends’ warnings, the victim gradually realizes the scam and takes action like reporting to the police.
- Example Dialogue:
- Friend: “Are you sure this is a real cop? There are tons of similar scams online—be careful!”
- Victim: “Something feels off—I’m going to the police.”
Conclusion
This case demonstrates how scammers use intimidation, forged documents, and psychological manipulation to lure victims into a trap and attempt to steal their money. With reminders from friends and personal reflection, the victim eventually recognized the scam and took steps like reporting it to the police to protect their rights. This case serves as a reminder to stay vigilant when receiving unknown calls, avoid trusting unverified information, and prevent becoming a victim of fraud.
Myanmar Transnational Fraud Syndicate Public Sentiment
Summary of Typical Cases
Wang Xing Incident
- Entrapment Trajectory: On December 24, 2024, Wang Xing spotted a Thai film crew recruitment post in an actors’ resource WeChat group. Driven by career aspirations, he added the casting coordinator “Yan Shiliu” on WeChat for an audition and secured an invitation to Thailand due to his strong English skills. Initially hesitant due to vague filming details and suspicious locations, he declined. However, after pressure from the crew, combined with the difficulty of landing roles and the prospect of overseas opportunities—and finding no red flags online—he decided to go. On January 2, 2025, he flew from Shanghai to Bangkok on a “non-immigrant visa,” booked a hotel in Phuket to learn more about the job, and arrived in Bangkok at midnight on January 3. He was picked up in a gray Toyota Altis sedan, which veered off course toward the Myanmar border. That morning, in Tak Province’s Mae Sot district, he switched vehicles, and a driver named Wichai (alias), under orders from a Karen ethnic male soldier, took him away. Wang Xing went missing near the Thai-Myanmar border in Mae Sot, Thailand, and was taken to Myawaddy, Myanmar, where he was forcibly shaved and subjected to coercive training.
- Rescue Process: After Wang Xing disappeared, his girlfriend Jiajia called Shanghai police at 11:54 on January 3 and simultaneously sought help from the Chinese Embassy in Thailand. At 22:37 on January 5, she posted a detailed plea for help on Weibo with key information and images, tagging celebrities to amplify the message, sparking widespread attention and accelerating rescue efforts. On January 6, Shanghai police opened a case, and his family reported it in Thailand. On January 7, Thai police used an automatic license plate recognition system to track the vehicle and, with local Myanmar assistance, rescued Wang Xing from a second detention site. He was flown back to Bangkok via police aircraft, returned to China on January 10, and arrived safely at midnight on January 11.
Extended Reading:
News Link 1 News Link 2 News Link 3 News Link 4
Hong Kong Woman Pang Xinying Incident
- Entrapment Chain: Pang Xinying, a Hong Kong actress, met an intermediary on social media claiming to offer high-paying jobs. Lured by promises of a bright career, she succumbed to the temptation of high salaries without recognizing the scam. She entered Thailand on December 27, 2024, and went missing the next day.
- Rescue Stalemate: After Pang Xinying disappeared, her mother received a ransom demand of USD 28,000 from the syndicate. Due to the syndicate’s refusal to clarify transaction terms, the ransom wasn’t paid, and Pang remains unrescued. Her mother revealed that a friend, Bingbing, is also missing.
Extended Reading:
News Link 1 News Link 2 News Link 3 News Link 4
Hong Kong Man Andy Incident
- Entrapment Process: Andy was hooked by a Thai gold-smuggling ad on social media promising quick, easy money. Struggling financially and eager for wealth, he contacted the “employer” and intermediary, fully convinced of the opportunity. He flew from Hong Kong to Bangkok as instructed, but was diverted to Mae Sot, Myanmar, where he was violently abducted and taken to the “Jiaoke Park” syndicate site.
- Rescue Challenges and Breakthrough: At “Jiaoke Park,” Andy endured over a month of physical punishment. His family scrambled to raise funds, ultimately paying HKD 400,000 in ransom to secure his release from the ordeal.
Extended Reading:
Other Similar Victim Cases
Following the exposure of the “Wang Xing Incident,” several similar transnational fraud and human trafficking cases surfaced, highlighting the syndicate’s extensive and complex operations:
- Actor Fan Hu: Lured by a fake film crew recruitment in an actors’ WeChat group, he auditioned online, received a satisfactory response and a salary raise promise, but sensed something off in Thailand and feigned compliance to escape back home.
- Actor Deng You: Became suspicious while applying for a passport and returned to China in time to avoid the scam.
- Model Yang Zeqi: Experienced a process similar to Wang Xing’s—audition, travel to Thailand, vehicle switches—and went missing on December 20, 2024.
- Missing Women Xu Haoning and Lin Meiling: Traveled to Thailand on December 27, 2024, and were taken to the Myawaddy Elephant Telecom Fraud Park in eastern Myanmar, losing contact. Recent media reports indicate they’ve escaped and returned home.
Extended Reading:
News Link 1 News Link 2 News Link 3 News Link 4
Decoding Fraud Tactics
Precision Entrapment Strategies
- Career Bait: Targeting actors, models, influencers, and others seeking overseas work and opportunities, the syndicate uses fake film crew recruitment, high-paying modeling gigs, or international collaboration projects as bait—such as the Thai film crew offer Wang Xing encountered—to cast a precise net. These professions often have high social visibility and diverse but unregulated job channels, which the syndicate exploits by blending seemingly legitimate offers into the mix to boost credibility.
- Psychological Manipulation: Exploiting victims’ career pressures (e.g., too many actors, too few roles), their hope for “shortcuts to success,” and their unfamiliarity with overseas environments and opportunities, the syndicate sweetens online auditions with promises and grand visions, lowering victims’ defenses and fostering trust in fake offers. They understand these groups’ urgency to succeed in competitive industries and their desire for breakthroughs, tailoring irresistible career prospects while leveraging victims’ ignorance of foreign risks to obscure the danger.
Covert Transfer Tactics
- Vehicle Relay: In Thailand, the syndicate uses multiple vehicles and transfer points—like Wang Xing’s switches between a gray Toyota Altis and Toyota Hilux Revo—to confuse tracking efforts. They meticulously plan routes using Thailand’s complex traffic networks and surveillance blind spots, arranging handoffs at various locations to create a tangled trail, thwarting police efforts and buying time for cross-border smuggling.
- Cross-Border Smuggling: Bypassing official checkpoints, they use remote paths or boats to smuggle victims from Thailand to Myanmar fraud parks, trapping them in a foreign predicament with little hope of self-rescue. The Myanmar-Thailand border features rugged terrain—mountains, jungles, rivers—that the syndicate navigates expertly, choosing hidden routes to evade border patrols and silently deliver victims to their destination, where escape becomes nearly impossible amid unfamiliar languages, environments, and armed guards.
Coercive Control Methods
- Physical and Mental Suppression: Forcing haircuts—like shaving Wang Xing’s head—destroys personal identity and psychological defenses, fostering submission; high-pressure training strips victims of basic needs, using hunger, exhaustion, and threats to compel compliance with telecom fraud tasks. These extreme measures physically torment victims while breaking their will, plunging them into despair and fear, leaving survival as their only option under syndicate control.
- Information Blackout: Seizing phones and passports cuts victims off from the outside world, severing legitimate help channels and leaving them isolated and at the syndicate’s mercy. Without communication tools, they can’t reach family or friends, and without passports, they can’t seek aid from embassies, becoming caged prey for the syndicate.
Transnational Collaboration Network
- Internal-External Collusion: The syndicate collaborates with Myanmar’s local armed groups and criminal organizations, leveraging eastern Myanmar’s chaotic situation to establish fraud park “strongholds” and operate with geographic advantage, evading crackdowns. Parts of Myanmar have long been under armed faction control with weak government oversight, enabling the syndicate to form symbiotic ties with local forces, gaining armed protection and using the chaos to mask their crimes, fortifying their transnational fraud empire.
- Middlemen Operations: Hiring stateless individuals like Wichai to handle key tasks—abduction, transfers—reduces exposure risks for core members, ensuring the crime chain remains covert and efficient. These middlemen operate outside formal societal systems, making them hard to trace, and even if caught, their obscurity shields the syndicate’s higher-ups, acting as an “invisible shield” for transnational operations.
Societal Impact Ripple Effects
- Entertainment Industry Turmoil: Actors, models, and others grow wary of cross-border work, with international opportunities shrinking due to fraud fears, stunting talent mobility and industry growth. Performances by stars like Eason Chan and Zhao Benshan in Thailand were canceled amid safety concerns, refund waves, and public pressure, damaging Thailand and Southeast Asia’s entertainment industry reputation.
- Related Information: News Link 1 News Link 2 News Link 3
- Public Trust Crisis: People grow highly skeptical of overseas job offers on social media and online platforms, especially in Southeast Asia, with “high-salary lures” losing credibility; tourists fear traveling to the region, worried about scams or abductions, dampening local tourism.
- Public Perception Bias: Some netizens display negative attitudes, blaming victims for greed or stupidity, attributing their plight to personal failings rather than the syndicate’s criminal nature or victims’ predicaments; regional prejudices emerge, framing fraud as a local issue rather than a transnational crime; others remain indifferent, seeing others’ misfortune as irrelevant, underestimating the issue’s severity; some mock the tragedy, ignoring its societal harm; extreme, impractical solutions reflect ignorance of international dynamics and enforcement complexities. These attitudes reveal a skewed societal understanding of transnational fraud, with many unaware of their own risks, limiting local vigilance and prevention efforts.
- Related Information: News Link 1 News Link 2 News Link 3 News Link 4 News Link 5 News Link 6 News Link 7
Key Figure Profiles
Crime Syndicate Structure
- Wichai (Alias) and Other Operatives: Thai executors hired by the syndicate, stateless and familiar with local terrain, they drive vehicles to transfer victims, deeply involved in human trafficking and telecom fraud’s front-end operations.
- Karen Ethnic Male Soldier: A senior strategist, possibly tied to local armed groups, with military command skills, orchestrating transnational crime processes and directing precise abductions and transfers for syndicate profit.
- “Yan Shiliu” and Management: Well-versed in entertainment industry tactics, they use fake crew recruitment to screen and lure victims to Thailand, feeding the fraud pipeline.
- “Boss Yu” and Top Brass: Suspected Chinese masterminds running “Apollo Glory” company and the “Apollo Park,” leveraging vast transnational fraud experience and resources to oversee every stage—entrapment, control, profit extraction—with absolute dominance.
- Internal-External Collusion: Partnering with Myanmar’s armed groups and criminals, they exploit eastern Myanmar’s turmoil to establish fraud bases, dodging crackdowns with geographic and political leverage, building a robust transnational fraud fortress through symbiotic local alliances.
Comprehensive Countermeasures
Industry Self-Strengthening Defenses
- Enhanced Vetting: Actors and agencies establish strict cross-border job vetting, thoroughly checking recruiters’ backgrounds, credentials, and project legitimacy to preempt risks.
- Training Empowerment: Industry groups bolster overseas work safety training, offering fraud prevention knowledge and skills to heighten practitioners’ self-protection awareness and capabilities.
Policy Reinforcement Support
- Transnational EnforcementCollaboration: China, Thailand, and Myanmar deepen cooperation with regular intelligence sharing, joint operations, refined enforcement agreements, and streamlined judicial collaboration to strike at crime’s roots.
- Border Control Upgrades: Thailand strengthens border patrols and surveillance, tightens entry-exit scrutiny, and combats illegal crossings and trafficking to fortify security.
Technology-Enabled Safeguards
- Surveillance Upgrades: Enhanced automatic license plate recognition, real-time tracking, satellite positioning, and drone patrols boost enforcement precision and coverage.
- Smart Warning Systems: Big data analysis uncovers fraud patterns, while AI modeling predicts suspicious behavior, aiding precise enforcement strikes.
Legal Framework Backbone
- Refined Unified Laws: The three nations jointly craft specialized transnational fraud laws, standardizing sentencing, clarifying crime definitions, and amplifying legal deterrence.
- Stricter Intermediary Oversight: Tight regulation of online recruitment and labor agencies, cracking down on false information and penalizing rogue entities to cut off fraud info sources.
Societal Care Shield
- Victim Support: Establish dedicated funds for financial aid, psychological counseling, and legal assistance to help victims and families recover.
- Public Awareness Boost: Governments, media, and organizations ramp up campaigns targeting perception biases with tailored strategies. On one hand, community outreach, online seminars, and short videos spread awareness of common fraud tactics, real cases, and harms, correcting regional biases and emphasizing transnational fraud as a global issue affecting all; on the other, they foster proper vigilance—like caution toward overseas job offers and verifying info authenticity—elevating public prevention capacity and forging societal consensus to tackle transnational fraud risks together.
Hong Kong Courier Scam Cases
Preface
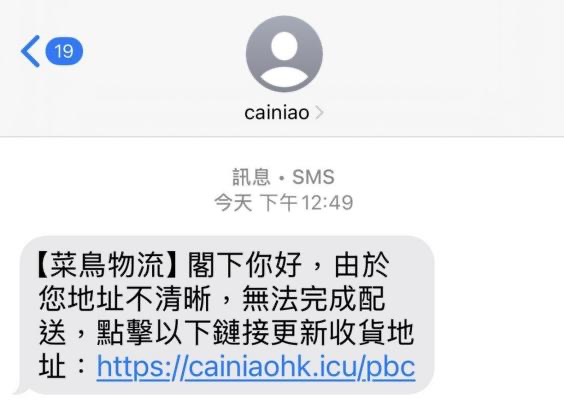
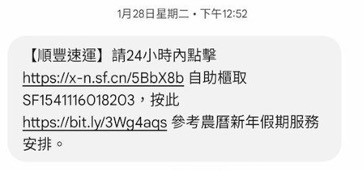
Recently, Hong Kong has seen multiple scam cases involving the misuse of well-known courier brands (such as "Cainiao" and "SF Express"). These scams employ tactics like phishing websites and fake text messages, resulting in the leakage of personal data and financial losses for citizens. In the last week of February, the police received 63 reports of related scams, with total losses exceeding HK$3.2 million, of which 45 cases involved fraudulent "Cainiao" SMS messages. A 43-year-old man, after entering his credit card details, was defrauded of over HK$120,000. This report will provide an in-depth analysis of the scam process, techniques, content characteristics, victim profiles, and psychological manipulation strategies to enhance public awareness and prevention capabilities.
Scam Process
Overview
These scam cases primarily involve fraudsters impersonating well-known courier brands like "Cainiao" and "SF Express," sending fake SMS or social media messages to trick recipients into clicking phishing links and entering personal and credit card information, ultimately stealing their money.
Key Stages
- Initial Contact
Scammers contact victims via SMS, WhatsApp, or email, falsely claiming there is an issue with their parcel (e.g., incomplete address) or that additional fees are required, urging victims to click a provided link. - Building Trust
The sender of the scam SMS appears as "cainiao" or a similar official-sounding name, with highly convincing language and interfaces, leading victims to believe the message is from a legitimate source. - Inducing Action
Victims click the phishing link and are directed to a highly realistic fake logistics website, where they input sensitive data such as personal information, credit card numbers, and bank account details. - Final Fraud
Scammers use the provided information to make unauthorized transactions, resulting in financial losses. In some cases, the stolen personal data is resold or used for further scams.
Scam Techniques
Scammers employ a variety of technical methods and social engineering tactics to make their schemes harder to detect.
Technical Methods
- Scammers use fake base stations to spoof SMS sender IDs, making messages appear as if they come from "cainiao" or other official sources.
- They design counterfeit websites with user interfaces (UI) nearly identical to official pages to deceive victims.
- Phishing links are distributed via SMS or social media channels to reach a wider pool of potential victims.
Timing of the Crime
Scam messages often appear during peak holiday shopping periods, such as "Double 11" or Christmas sales seasons, capitalizing on heightened public attention to logistics updates to enhance the credibility of the scam.
Sophisticated Social Engineering
Scammers may use partially obtained personal information (e.g., names or addresses) to conduct targeted fraud, increasing their success rate.
Characteristics of Scam Content
Common Phrasing and Language Patterns
- "Your parcel address is incomplete, please click the link to update your information."
- "Additional shipping fees are required, or delivery cannot proceed."
- "Your parcel will be returned due to incorrect information."
Scam pages typically prompt users to enter sensitive information such as names, addresses, and bank card details, disguised as payment verification pages.
Keyword Analysis
Frequently used keywords: incomplete address, update address, handling fees, credit card number, impersonation, phishing link, delivery failure.
Scammers exploit the urgency of logistics delivery, pressuring victims to act quickly without verifying the information.
Victim Profile Analysis
Main Characteristics
Victims are typically frequent online shoppers, including young people, working professionals, and users who are familiar with but not highly skilled in cybersecurity. Many rely on social media for courier updates and are accustomed to receiving logistics notifications via SMS or WhatsApp.
Psychological Vulnerabilities
- Heavy Reliance on Online Shopping: Victims are used to receiving logistics notifications and may overlook fake messages.
- Anxiety Over Delivery Delays: Scammers exploit victims’ urgency to receive parcels, creating a sense of pressure.
- Trust in Authoritative Brands: Scam messages mimic reputable courier brands, lowering victims’ guard due to brand familiarity.
- Habit of Clicking Links: Victims click without verifying the source.
Psychological Manipulation Strategies
Scammers influence victims’ decision-making to trap them through various methods:
- Fear and Urgency
Using phrases like "Failure to update your address in time will result in your parcel being returned" or "Your delivery may be sent back" to create unease and urgency. - Trust and Authority
Forging brand names and mimicking official interfaces to instill a sense of security and reduce suspicion. - Scarcity Effect
Pressuring victims with "Update within 24 hours" or "Pay fees within a limited time" to prompt immediate action. - Social Proof
Potentially using fake reviews or fabricated victim stories to create the illusion that many have successfully "updated their information," boosting credibility.
Sources of Analysis
This report analyzed relevant social news reports and 72 related posts from the social media platform Xiaohongshu (Little Red Book).
Media Reports
- "Hong Kong Man Loses HK$120,000 After Trusting Fake ‘Cainiao’ SMS"
HK01 - "Fake SF Express Scam SMS: Netizens Highlight Two Major Red Flags"
HK01
Selected Social Media Posts
- "Hong Kong’s New Scam Exposed: HK$3.2 Million Lost!"
Xiaohongshu - "Urgent Warning! Don’t Click This Type of Courier SMS!"
Xiaohongshu - "Courier Scam SMS Pretending to Be SF Express – Don’t Fall for It!!!"
Xiaohongshu
Prevention Tips
- Verify Information Sources
When receiving messages requesting personal or financial information, contact official customer service directly for confirmation instead of clicking unknown links. - Pay Attention to SMS and Link Details
Legitimate logistics companies typically do not ask users to enter sensitive information, such as credit card details or address updates, via third-party websites. - Install Security Software
Enable SMS filtering functions to block suspicious messages.
Conclusion
The core tactic of Hong Kong courier scams is exploiting victims’ trust in logistics information and their sense of urgency, using technical methods and social engineering strategies to perpetrate fraud. The public should remain vigilant, verify information sources, and avoid clicking unknown links. Governments and businesses should also enhance awareness campaigns and technical safeguards to reduce the risk of citizens falling victim.
When receiving any message requesting personal information or payment, always stay cautious, carefully verify the source, and ensure the safety of your personal assets.
Public Opinion Report on Telecom and Online Financial Scams in Hong Kong
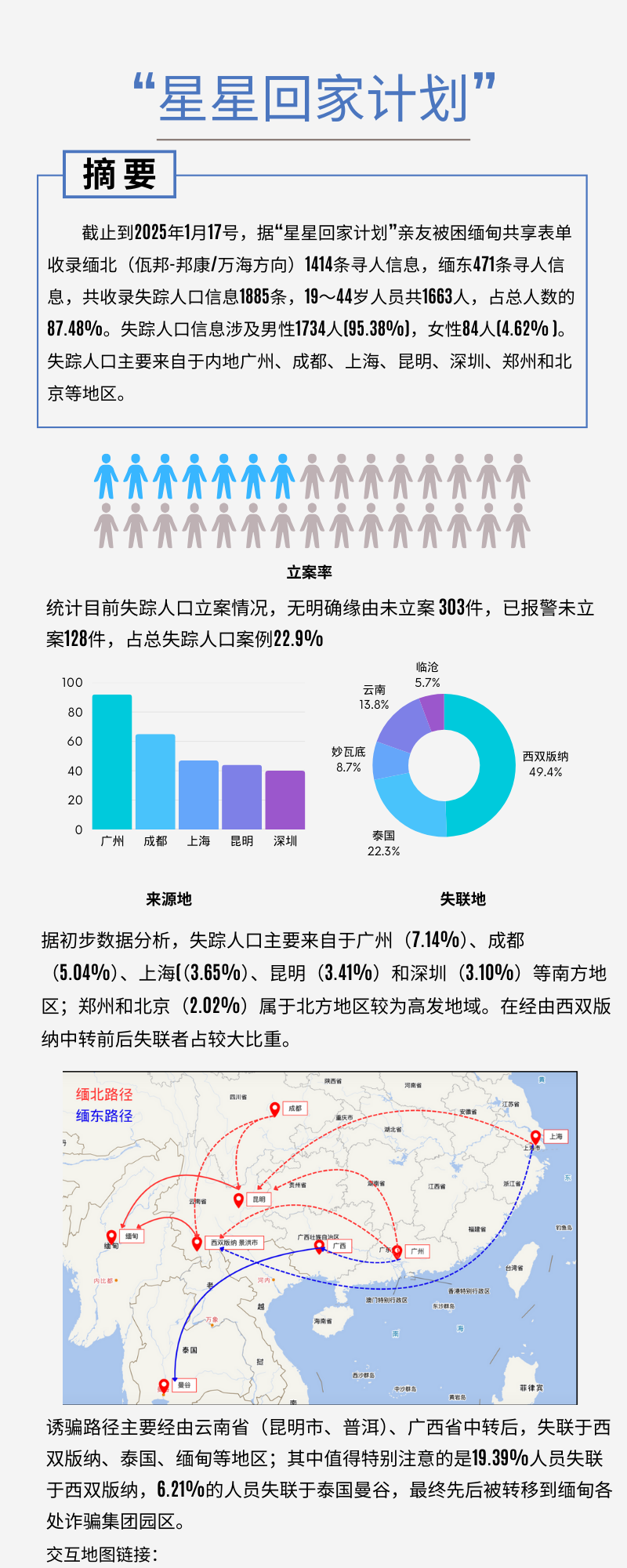
"Star Homecoming Project": Thousands of Families Trapped in Myanmar Await Hope
An online document records information on thousands of missing persons, each name representing a life ensnared in the telecom fraud zones of northern and eastern Myanmar.
1885
Total Missing Persons
87.48%
Aged 19-44 Proportion
22.9%
Cases Not Filed
95.38%
Male Proportion
(Data as of January 17, 2025)
Project Origin: From Individual Ordeals to Family Solidarity
The "Star Homecoming Project" began in January 2025 as an online document created by victims' families to collect information on individuals trafficked to Myanmar's telecom fraud zones and to promote greater attention and rescue efforts.
It all started with the publicized case of actor Wang Xing, who was deceived into traveling to Myawaddy's fraud zone for a job opportunity. After his rescue and return, more victims' families began stepping forward to seek help.
Data Insights: Profile of Telecom Fraud Victims
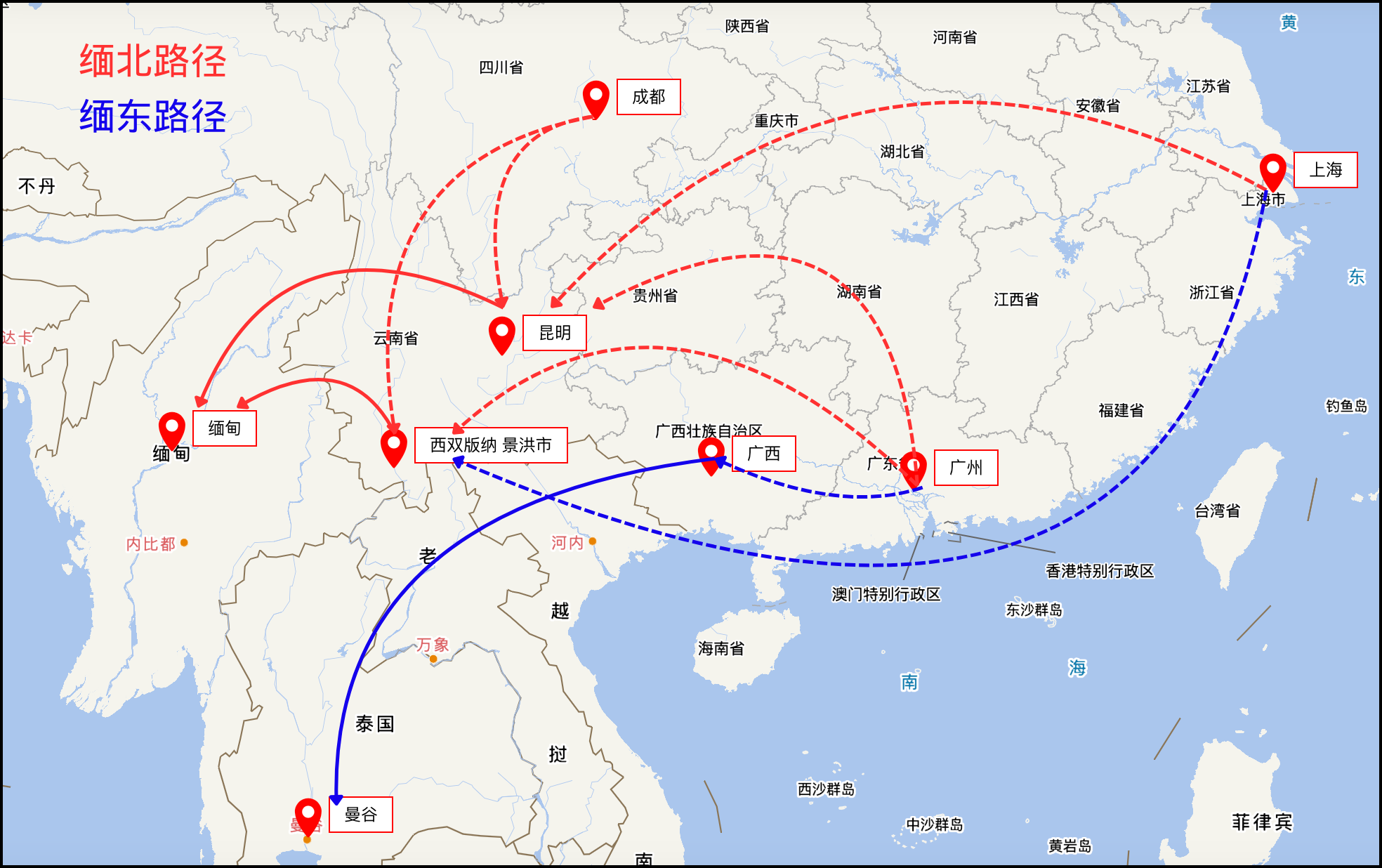
- Northern Myanmar Missing Persons: 1,414 cases
- Eastern Myanmar Missing Persons: 471 cases
- Total Missing Persons: 1,885 cases
- Persons Aged 19–44: 1,663
- Male Missing Persons: 1,734 (95.38%)
- Female Missing Persons: 84 (4.62%)
- Unfiled Cases Without Clear Reason: 303
- Reported but Unfiled Cases: 128
Missing Persons Path Analysis
Deceptive Tactics: From High-Paying Job Lures to Violent Abduction
High-paying job offers are the primary deception tactic, accounting for nearly 70% of cases. Victims are often lured with promises of work or profit, such as acting, purchasing, loan facilitation, or partnerships.
Deceptive methods are becoming increasingly sophisticated, making them hard to detect. For instance, a lawyer was invited by a client to conduct due diligence in Thailand, with all travel expenses covered.
Arduous Journey Home: Filing Challenges and Rescue Obstacles
For victims' families, the road to rescue is fraught with difficulties, with filing a case itself being a significant challenge.
Adults often face case rejection due to insufficient evidence, while cases involving university students or minors have a higher likelihood of being filed.
Distribution of Missing Persons' Origins
- 7.14% Guangzhou
- 5.04% Chengdu
- 3.65% Shanghai
- 3.41% Kunming
- 3.10% Shenzhen
- 2.02% Zhengzhou
- 2.02% Beijing
Main Areas of Disappearance
- 49.4% Xishuangbanna
- 22.3% Thailand
- 13.8% Yunnan
- 8.7% Myawaddy
- 5.7% Lincang
High-Risk Transit Routes
Deceptive routes mainly pass through Yunnan Province (Kunming, Pu'er) and Guangxi Province, with disappearances occurring in Xishuangbanna, Thailand, and Myanmar.
19.39% of individuals disappeared in Xishuangbanna, and 6.21% in Bangkok, Thailand.
Prevention Guide: Eight Principles to Protect Yourself
- Don't Be Greedy: If something seems too good to be true, it probably is.
- Don't Be Arrogant: Educated individuals need to be especially cautious and avoid overconfidence.
- Don't Trust: Be wary of any paid tasks involving travel to dangerous areas for errands or deliveries.
- Don't Engage: When traveling in Southeast Asia, avoid unfamiliar companions.
- Don't Be Naive: Don't accept kindness from strangers.
- Don't Be Careless: Avoid recklessness and don't rely on luck.
- Don't Be Ignorant: Learn about victims' tragic experiences and the darker side of human nature.
- Don't Travel Abroad: For work or vacation, prioritize domestic options and avoid leaving the country.
Data Statistics Report
Below is a partial data analysis and chart for the "Star Homecoming Project":
Conclusion
These missing persons' data not only reveal the severity of transnational telecom fraud but also highlight new challenges to the safety of Chinese citizens abroad. With intensified international cooperation and increased public awareness, we hope the trapped individuals can return home soon, and such tragedies will not recur.
Cambodia-Thailand Cross-Border Gambling Network Map: A Gray Profit Chain Worth Billions of Baht
Introduction
In the border region between Thailand and Cambodia, a cross-border gambling empire worth billions of baht operates discreetly, reshaping the local economic ecosystem and fostering crime and corruption.
According to the Thailand Gambling Problem Research Center, escalating tensions along the Thailand-Cambodia border have revealed a vast power network spanning politics, military, and business, establishing a transnational casino empire with a complex web of interests.
Casino Empire Map
Cambodia’s booming casino industry reflects complex international relations and power structures.
- Over 150 legal casinos are spread across Cambodia, surpassing Macau and Las Vegas.
- 70% of Poipet’s economic activity relies on casino revenue.
- These casinos support approximately 200,000 Cambodians.
Interplay of Power and Money
The casino empire operates through a network of power and profit-sharing, involving high-level political and business elites.
- Cambodian-Chinese senator, "Lord Sia Pad," controls a resort casino in Koh Kong Province.
- Through his Lia Shaoliang Group, he manages casinos, hotels, and industrial zones.
- His close relationship with former Cambodian Prime Minister Hun Sen is notable.
Hidden Operating Mechanisms
The casino empire relies on a system of shadow ownership and power collusion for discreet profit distribution.
- Most casinos operate through "nominal ownership" structures.
- Local Cambodian elites participate by providing land as capital.
- Former Khmer Rouge leader Sang Pho collaborates with casinos in his territory.
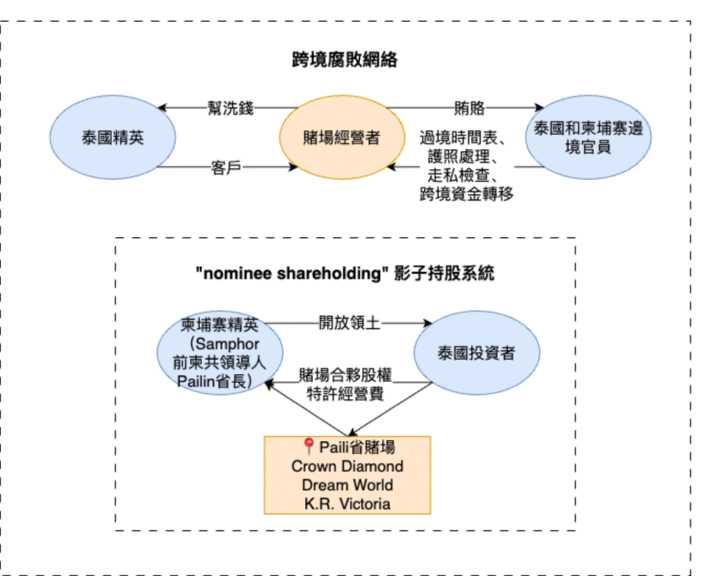
Figure 1: Cross-Border Corruption Network and Shadow Ownership System - Power Structure Analysis Using Knowledge Graph Technology
From Gambling to Telecom Fraud: Industry Evolution
This gray industry chain has evolved, expanding from gambling to telecom fraud and modern slavery.
- In 2025, cross-border gambling siphoned 18.4 billion USD from Thailand.
- Over 23,000 telecom fraud operatives relocated to Cambodia, turning casinos into fraud and money-laundering bases.
- The U.S. Treasury Department sanctioned networks stealing nearly 10 billion USD.
Poipet Gambling Hub and Exposed Incidents
Cambodia hosts around 150 casinos, making it Southeast Asia’s gambling capital, mostly along the Thai border.
The largest hub, Poipet in Banteay Meanchey Province, opposite Aranyaprathet District, sees 80% of gamblers as Thai nationals.
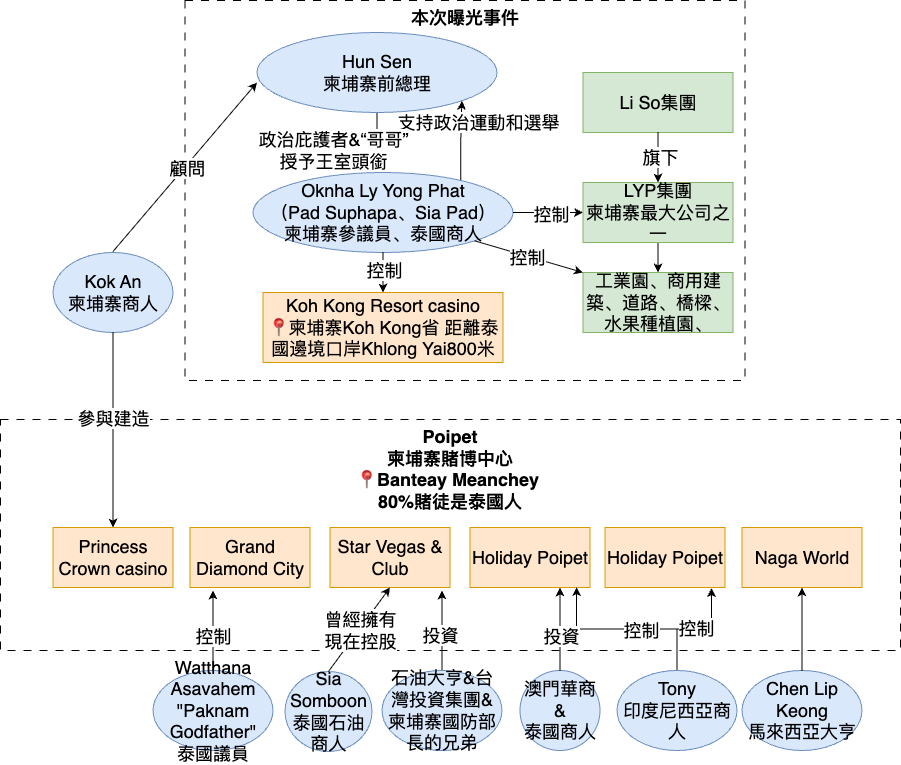
Figure 2: Poipet Gambling Hub and Power Network - Interest Relationship Analysis Using Large Language Models
Border Tensions and Economic Warfare
The Thai government initiated an economic war targeting the gray industry.
- In early 2025, Thailand implemented a "three-cut" strategy in Poipet: cutting electricity, internet, and fuel.
- Cambodian casinos reliant on Thai infrastructure were paralyzed.
- Cambodia closed the Thai-Cambodian border crossing, causing 500,000 Cambodian workers to lose jobs.
International Sanctions and Responses
The international community has intervened, targeting this gray industry with precision strikes.
- On September 8, 2025, the U.S. Treasury Department sanctioned 10 Cambodian entities.
- These include Chinese businessmen naturalized in Cambodia, banks, and Sihanoukville casinos.
- They were accused of supporting virtual currency fraud centers run by Chinese criminal groups.
Victims’ Real Experiences
Behind the massive figures and political games lies the tragic fate of ordinary people consumed by the gray industry.
In October 2025, two Thai men were arrested in Aranyaprathet District, Sa Kaeo Province, after illegally crossing from Poipet, Cambodia. Lured at Bangkok’s Mo Chit Bus Terminal to open "money mule" bank accounts, their phones and IDs were confiscated by Chinese employers, who detained them for facial scans used in transactions. They received only 1,000 baht over two weeks.
Future Trends and Regional Impact
This battle over the border casino empire could reshape Southeast Asia’s gray economic ecosystem.
- Thailand’s Entertainment Complex Bill aimed to open legal casinos in Bangkok, projecting 5.5 billion USD in annual tax revenue and 15,000 jobs.
- The plan was halted due to opposition from Thai Buddhist forces.
Analysis Method Explanation
This case uses large language models to analyze text data, identifying key entities and patterns, and knowledge graph technology to map the cross-border gambling network’s power structures and interest flows.
References
The Billion-Baht Casino Empire: How Thai-Cambodia Border Tensions Expose Hidden Networks of Power - The Nation Thailand
